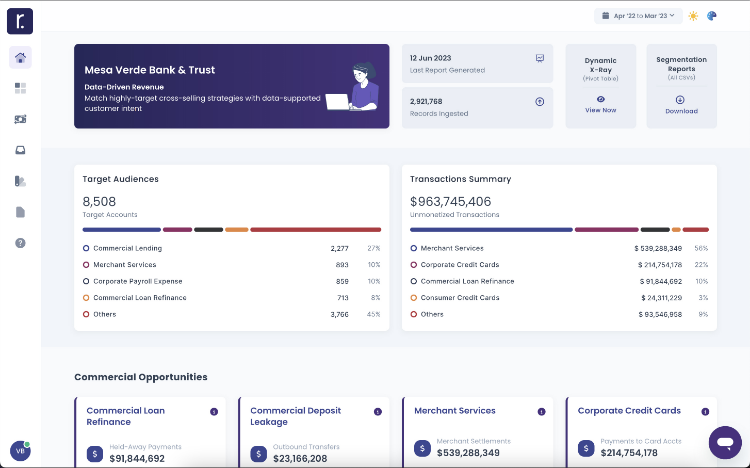
Uncover key insights. Prioritize opportunities + take action.
Actionable insights at every banker’s fingertips. Uncover growth opportunities and prioritize actions to grow customer relationships.
Unlock insights by bypassing legacy infrastructure limitations. Ingest data from multiple sources and overcome data quality barriers.



Tangible results.
Bank opportunity case study spanning 16 banks + $50 billion in aggregate deposits.
What our partners say.

The Revio platform has enabled our commercial bankers to be far more aware of growth potential with our existing clients and has helped us prioritize efforts. Because of that, we’re focused in the right places and winning more deposits and business with both new and long-term clients.“
– Carson Lappetito
President, Sunwest Bank

Revio’s ability to unlock insights in our data will help our bank remain competitive and relevant in today’s ever more challenging financial service marketplace.“
– Greg Ohlendorf
President & CEO, First Community Bank and Trust

Our partnership with Revio will enable us to identify customer needs and will help us grow our relationships with our customers. Equipped with a greater understanding of our clients, we can approach them with more personalized solutions.”
– Justin Dunmyer
Chief Digital Officer, Citizens State Bank
Banking & Funding Partners





Hit Go on Growth
Place critical customer insights into the hands of your growth-owning team members and transform your customer’s banking experience for the long-haul.